Can Email Be Spoofed at Office Network Level? Here’s How to Guard Against It
Introduction
Even with a clean, secure mail server, your office network isn’t immune to spoofed email attacks. This blog explains how spoofing works, why it’s a threat—even internally—and how to strengthen your defenses.
What Is Email Spoofing?
Email spoofing is when the From header in an email is forged, making it look like it originated from someone else. Attackers don’t need access to your mail server—just the ability to send SMTP messages.
- External Spoofing: Malicious actors forge emails from outside your network, impersonating internal accounts.
- Internal Spoofing: A compromised workstation or rogue user sends spoofed emails directly on your LAN.
Why Spoofing Works (Even on Secure Servers)
- SMTP is trust-based: “From” fields can be manipulated without server compromise.
- Weak email auth: Missing or misconfigured SPF, DKIM, or DMARC makes spoofing easier.
- Human error: Users may trust internal addresses without verifying headers.
🛠️ SPF, DKIM & DMARC: Your Shield
Implementing email authentication protocols prevents spoofed messages:
| Protocol | What It Does | How It Helps |
|---|---|---|
| SPF | Authorizes sending IPs via DNS records | Rejects emails from unauthorized sources |
| DKIM | Adds cryptographic signature via DNS | Verifies message authenticity and content integrity |
| DMARC | Enforces SPF/DKIM alignment, decides actions on failure | Quarantines or rejects spoofed emails |
📌 DMARC must reach a policy of p=reject to effectively block spoofing.
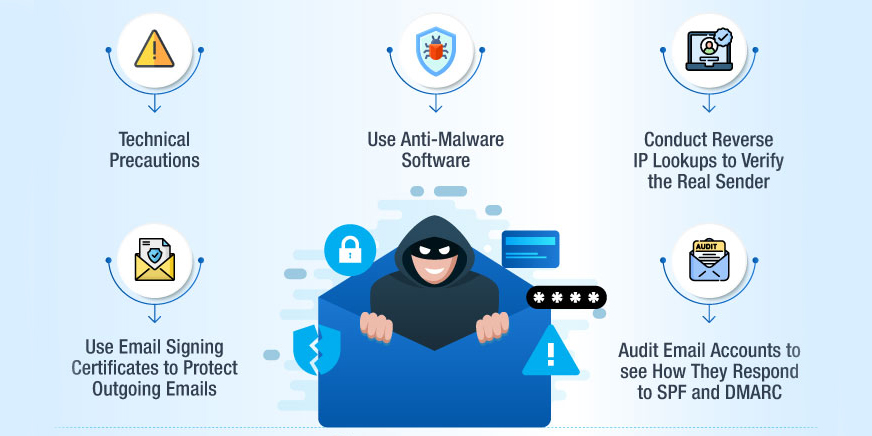
Steps to Prevent Office-Level Spoofing
- Deploy & Enforce SPF, DKIM & DMARC
- Start DMARC in monitor mode then tighten to reject.
- Restrict outbound SMTP on your LAN
- Only allow emails through your mail server or gateway.
- Use email security gateways with spoofing detection.
- Monitor logs & networks for unauthorized SMTP activity.
- Train staff to verify emails—even from internal senders.
- Regularly scan all workstations for viruses and malware
- Compromised endpoints can be used to send spoofed or malicious emails.
- Enforce regular password changes for email and network logins
- Reduces the risk of attackers misusing stolen credentials for internal spoofing.
Internal Network Controls
- Segment workstations from emailing ports.
- Log all SMTP traffic: detect unexpected relay attempts.
- Use secure email appliances with content inspection.
In Summary
Even a secure server doesn’t eliminate spoofing risk—because the office network itself can become an attack surface. The combination of SPF, DKIM, DMARC, robust network restrictions, antivirus hygiene, strong password practices, and user awareness offers layered protection against spoofed messages.
Conclusion
To truly secure your email environment, treat office email spoofing prevention as a network concern. Combine technical safeguards with policy and awareness to defend both incoming and internal threats.
